Kubernetes solves container issues by providing an extensible, declarative platform that automates the management of containers for high availability, resiliency, and scale. But, Kubernetes is a big, complex, fast-moving, and sometimes confusing platform that requires users to continually learn and acquire new skills.
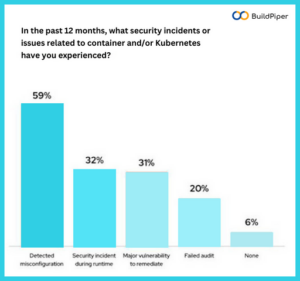
Apart from Kubernetes deployment, Kubernetes security has become an issue of serious concern now. With so much complexity in deploying Kubernetes, unwanted exposure tends to increase, making Kubernetes vulnerable to security threats and unauthorized access. This ultimately increases the number of profound Kubernetes challenges for teams and enterprises.
Before reading further, please refer to the first part of this blog where we’ve talked about security in Kubernetes. In the previous blog: “The Abstruse Case Of Handling Kubernetes Security- Part 1”, we covered one security challenge in Kubernetes. Here, in this blog, we’ll discuss the other two Kubernetes security challenges faced by enterprises and software teams while setting up and deploying Kubernetes clusters. So, let’s take a quick look at this Kubernetes security checklist to avoid security breaches and attacks.
Managing Configurations of Cluster Workload
In addition to managing the configuration of the Kubernetes cluster, enterprises need to manage the configurations of all the workloads that are running on the cluster. Perhaps, it is one of the most significant Kubernetes security challenges faced by enterprises and teams. An open-source tool such as Helm charts can be used to automate application provisioning and configuration for Kubernetes as well as to deploy simple or complex applications made up of several separate services.
However Helm is very useful for managing Day 1 operations, it fails to manage Day 2 operations, which is where Kubernetes operators are of premium importance. Operators are software extensions to Kubernetes that make use of custom resources to package, deploy and manage complex applications designed to run on Kubernetes and their components. Operators accept human operational knowledge and encode it into the software that is packaged with the application and shared.
As already known, Kubernetes is designed for automation. Out of the box, Kubernetes provides built-in automation for deploying, running and scaling workloads. However, some workloads and services require an in-depth knowledge of how the system should behave beyond the conventional core capabilities of Kubernetes functionality.
Operators are purpose-built with functional intelligence to manage such applications. With easy-to-use Kubernetes APIs and tools, Kubernetes operators can help teams with secured deployment and streamlined Day 1 and Day 2 operations. Helm Charts can also be encased in a Kubernetes operator and used together.
When it comes to Kubernetes security, operators ensure that services deployed on Kubernetes maintain supported cluster configurations. In case, an unsupported configuration is made to a deployed service, then operators can reset the service to its original declared configuration. The best part of the story is Kubernetes operators can also be used to manage Kubernetes itself, making it easier to deliver and automate secured deployments.
Image Credits: Kubernetes Security Survey 2022
Managing Multi-Tenant Clusters
As Kubernetes scales, it becomes more and more difficult for teams to manage all workloads deployed on Kubernetes clusters and the clusters themselves. Multi-tenancy is one of the most effective ways to handle all of this. In fact, Kubernetes’ support for multi-tenancy brings its own advantages as it is a less expensive way of sharing cloud resources and a better way of utilizing resources.
But, what is multi-tenancy? Let’s read about this in detail! Clusters can be shared in many ways. In some cases, different applications may run in the same Kubernetes cluster. While in other cases, multiple instances of the same application may run in the same cluster, one for each end user. Such types of resource sharing are described using the umbrella term “Multi-tenancy”. In simple words, multi-tenancy is when multiple users share a single cluster.
[Good Read: 3 Tools To Automate Your Kubernetes Cluster Deployment]
Multi-tenancy introduces special Kubernetes challenges when it comes to resource sharing and security. Each workload must be isolated so that a security vulnerability or breach in one cluster workload doesn’t dribble into another. Likewise, each workload must have the right access to the computing, networking, and other resources provided by Kubernetes. So, let’s walk through these Kubernetes security best practices and strategies for addressing multi-tenancy issues and challenges.
- Namespaces
Namespaces work like sub-divisions or folders within a cluster and enable the management of access control, resource limits, and quotas. It allows organizations to isolate multiple teams within the same physical cluster when used with RBAC and network policies thus helping in segregating different workloads. This ensures that each workload has its own identity and can be configured with an appropriate security policy. - Role-Based Access Control (RBAC)
Role-based access control (RBAC) is an approach to restricting access to a computer or network resources based on the roles of individual users within an organization. It determines whether a user is allowed to perform a given action within a cluster or namespace. - Resource Quotas
ResourceQuota is an object in Kubernetes that limits aggregate resource usage and consumption per namespace which makes systems less vulnerable to attacks such as denial of service. By default, all resources within a Kubernetes cluster are created with unconstrained CPU and memory requests/limits. - Network Policy for Micro-Segmentation
It specifies how different groups of pods communicate with each other and other network endpoints. Policies defined are namespace-scoped. By default, if no policies are set in a namespace, ingress and egress traffic is allowed to move to and from pods in that namespace.
These strategies when applied with appropriate Kubernetes Security tools can help in resolving security issues while setting up and deploying Kubernetes.
Final Note: Balance Security and Agility
The pressure is on for enterprises to constantly innovate and deliver the best which makes it easy to treat security as an afterthought. Ideally, security is built into the later stages of the DevOps cycle, but organizations will benefit by explicitly adding “security” into the middle of DevOps—or by ingraining as much security automation in form of CI gate checks and CI analysis into the pipeline as possible.
To ensure that app development organizations can implement Kubernetes security best practices, take a step back and re-examine your CI/CD pipelines. Is your team using automated functional tests and executing comprehensive CI analysis? Are automated CI checks and security gates such as integrated vulnerability scanners integrated into the deployment pipelines? If not, then it’s time to think over these Kubernetes security checklists for ensuring a secured release!
To ensure security in Kubernetes, considering a DevSecOps platform such as BuildPiper or Kubernetes security tools can help in the secured cluster management and its deployment.
To explore other interesting features of this Kubernetes & Microservices App Delivery Platform, schedule a DEMO NOW!