With DevOps security becoming mainstream, business organizations have recognized the need for bringing security and development together. Enterprises are making their best efforts to find the right DevOps security tools & practices for better automation and sharing security responsibilities with development teams.
However, IT and DevOps experts who dive into the DevSecOps market looking for options, quickly realize that the number of DevSecOps tools and frameworks is so vast that it’s quite confusing to decide which one to choose. You can look at these best practices for implementing DevOps security to fix this problem. Here, in this blog, we’ll talk about,
- Best Practices for implementing DevSecOps
- Implementing DevSecOps from GroundUp
- BuildPiper– The most powerful DevSecOps Platform
Best Practices for Implementing DevSecOps
Select Tools that can Manage & Understand all Artifacts Natively
Before DevOps teams even get to the task of identifying which components of the software have vulnerabilities, they first need a versatile DevOps platform. A platform that can manage & store all the artifacts and binaries in a main single place, regardless of their type and technology. The DevOps platform needs to know the basic software requirements for execution. They also need to know which artifacts are being used or built & what their dependencies are.
Support for Containers & Cloud-Native Frameworks
Teams should go for solutions that support container-based release frameworks, which are fast becoming the de facto standard for cloud-native deployments. An in-depth and recursive understanding of container technology and the ability to dive deeply into each layer ensures that no vulnerability gets overlooked or ignored. Strike off security and scanning tools that don’t support containers, or don’t understand enough about their different layers and transitive dependencies.
Read our newly released eBook on DevSecOps to know more about its inception and growth!
Automate Governance
DevOps & SRE teams should have the power to automate governance of the complete system in cooperation with the security department. A governing system must be able to automatically enforce company policies and take the necessary action as and when needed without intervention. Key features of such an automated security system should include:
- Notification of security or compliance violations via different channels, such as email, instant messages and Jira tickets.
- Blocking downloads that contain spam or malicious content.
- Failing builds that depend on vulnerable components.
- Prevention of the deployment of vulnerable product releases.
Extend across the Pipeline
An incredible differentiator in DevSecOps will be a solution that can extract data and connect it to the security scans of all the binaries across repos, builds and containers. A platform which can continuously identify & monitor vulnerabilities, even after deployment. This way it will get noticed and accepted in the market.
Choose a Hybrid Solution
Business organizations that are not maintaining a hybrid infrastructure yet, will have to choose a hybrid solution in future. Therefore, selecting DevSecOps tools and solutions, at present, that would support their continuing cloud journey and hybridization of business infrastructure in future, would be the right choice. Doing this will ensure consistency & standardisation across DevSecOps pipelines, no matter in which environment they may be.
Implementing DevOps Security from Ground Up
DevOps security is a way to build security into an application, and the transition from existing CI/CD & DevOps processes to DevSecOps can be made easier with the right approach. The successful transition depends on breaking down the resistance to security practices that exist in many organizations. A “start small and start early” policy to improve security is recommended where new techniques, processes and tools, such as SAST and SCA, can be integrated with less downtime and cost.
Most importantly, you must decide what the success factors are before you start. Measuring success and the ROI of the effort is needed to build & grow DevSecOps within the organization. Tools and automation just provide the data needed to show progress, but communicating the ROI needs to be done in business terms. In the end, success results in more secure software and reduces your company’s exposure to data breaches, vulnerabilities, and cyberattacks.
BuildPiper- The Most Powerful DevSecOps Platform
By incorporating these DevSecOps practices in the build & deploy pipelines, businesses can easily prevent high risks and ensure a secured and hassle-free delivery. To make this happen, enterprises need DevSecOps tools that rightly fit into their business model. One such DevSecOps platform that can help enterprises with a smooth and quick set-up of CI/CD pipelines along with secure, seamless and compliant Microservices & Kubernetes management could be BuildPiper.
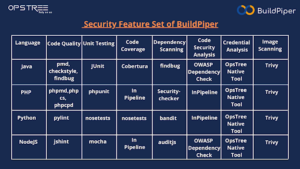
Here’s how this DevOps security tool assists in building CD pipelines enabled with comprehensive CI analysis and customizable CI gate checks for Macro & Micro builds and deployments. Let’s take a look at some of the security features offered by this Microservices & Kubernetes delivery platform,
Automated CI Checks
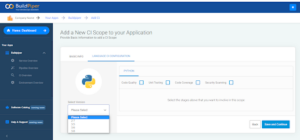
BuildPiper has automated & customized CI gate checks that support multiple language configurations.
Comprehensive CI Analysis
BuildPiper supports complete CI analysis allowing users to choose multiple stages which can be included in the CI Scope.
- Code Quality
- Unit Testing
- Code Coverage
- Code Security
BuildPiper uses the following frameworks and tools for CI analysis in different languages.
Secrets Management via Hashicorp Vault
BuildPiper supports seamless secret management with easy manageability of production-ready microservices. It has an out-of-the-box ability to manage the security of platform operations with ease via tools such as Hashicorp Vault.
Docker Image Scanning Process
BuildPiper involves the image scanning process as a part of the continuous integration/continuous delivery (CI/CD). Vulnerability scanning allows development teams to identify vulnerabilities in container images. This enables teams to fix these issues before using or pushing the image to Docker Hub or any Docker registry. This helps in secured deployments.
RBAC
BuildPiper supports Kubernetes role-based access control (RBAC). Kubernetes RBAC controls the access authorization. It also restricts access to a cluster’s Kubernetes API servers, both for service accounts and for users in the cluster. Besides providing these DevSecOps features, BuildPiper has the ability to run zero-touch, fully -automated & secured build & deploy pipelines. Additionally, the platform helps in making Kubernetes- Microservices application ready!
Key Takeaway
Security is an important aspect that needs to be taken care of right from the start. Ignoring potential security risks can expose applications to damaging threats leading to serious consequences. Considering the right DevOps security tools and effective practices can fasten the delivery process and help businesses with enhanced agility and greater ROI.
DevSecOps Platforms such as BuildPiper can enable this out of the box and make your Kubernetes & Microservices Journey, hugely rewarding!
Explore the other interesting features of this K8s cluster management platform including Managed Microservices, Managed Kubernetes, Secure Setup of delivery pipelines, and Security Compliance & Observability. To discuss your critical business scenarios and security concerns, Schedule a Demo NOW!
Watch our Walkthrough Videos to understand BuildPiper and its functionalities.