ConfigMaps & Secrets
After filling in the Access Level and Resource Quota details, you can enter the "Configuration and Secrets" details. Providing Configuration, Secrets and PVC details is not mandatory. It is completely optional to fill in details for this section.
The manageability of production-ready services becomes very simple with pre-configured features such as Config Maps and Secrets Management. Here's how BuildPiper enables all of this!
Before understanding how BuildPiper enables this all, we must know about Kubernetes Volume, Volume Mount, Volume Mount Path, ConfigMaps, Secrets, and PVC. Let's read about these here.
What is Kubernetes Volume?#
In Kubernetes, volumes are abstractions that represent a source of storage that can be mounted into a container. There are many different types of volumes, including
- hostPath volumes mount a file or directory from the host node's filesystem into the Pod.
- emptyDir volumes that are created when a pod is created and deleted when the pod is deleted.
What is Volume Mount?#
Volume mount is a feature in Kubernetes that allows you to mount a storage volume into a container in a pod. This provides a way to persist data that is generated or used by a container, even if the container itself is deleted or recreated.
What is Volume Mountpath?#
To mount a volume into a container, you define a volumeMount in the container definition. The volumeMount specifies the name of the volume to be mounted, and the path within the container's file system where the volume should be mounted. The volume and the volumeMount must be defined in the same pod definition.
What are ConfigMaps?#
Many applications rely on configurations which are used during either application initialization or runtime. ConfigMaps are the Kubernetes way to inject application pods with configuration data. They are Kubernetes objects that allow you to store configuration data separate from the container images. They can be used to manage environment variables, command-line arguments, or configuration files for your applications running in Kubernetes.
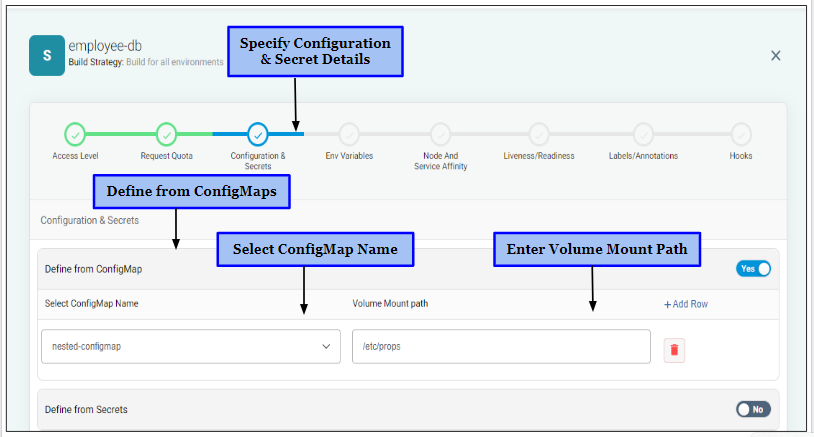
Mount ConfigMap in your Application#
If a ConfigMap is already onboarded in an environment and you want to mount the ConfigMap file on a particular Volume Mount Path, you need to follow these simple steps,
- Click “Yes” to define ConfigMap details else click “No”.
- Select the ConfigMap Name to choose the ConfigMap file.
- Specify the Volume Mount Path on which you want to mount the ConfigMap file.
- Click “Add Row” in order to specify more details regarding ConfigMaps.
What are Secrets?#
Secrets are Kubernetes objects that are used to store sensitive information, such as passwords, API keys, and certificates, separate from the container images. They can be consumed by pods through environment variables or mounted as files in a volume, and can be referenced in Kubernetes manifests using the Kubernetes API or command-line tools.
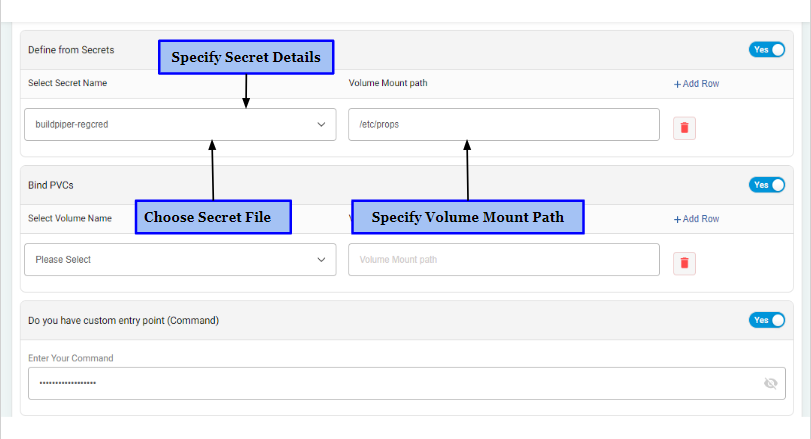
Define from Secrets#
Here’s how you can mount a Secret file on a specific Voume Mount Path. Basically, you need to create a volume that references the Secret, and then mount the volume on the desired Volume Mount Path in the container.
- Click “Yes” to define Secret details else “No”.
- Select the Secret’s name to choose the Secret file.
- Specify the Volume Mount Path on which you want to mount the Secret file.
- Click “Add Row” in order to specify more details regarding Secrets.
What is Persistent Volume Claim (PVC)?#
A Persistent Volume Claim (PVC) is an object in Kubernetes that represents a request for storage resources. A PVC is used to request a specific amount of storage from the cluster, and it can be mounted as a volume in a pod. The PVC acts as an intermediary between a pod and the underlying storage backend. When a pod is created and requires storage, it can request storage resources by creating a PVC.
Binding a PVC#
The Kubernetes control plane will then bind the PVC to a Persistent Volume (PV), which is a physical piece of storage in the cluster. Once the PVC is bound to a PV, the pod can access the storage resources and use the PVC as a volume mount in the pod specification.
How to Bind PVC?#
Follow these steps to bind a PVC specifying the Volume Name and Volume Mount Path.
- Click “Yes” to bind PVC else “No”.
- Select the Volume name with which PVC is mounted as a volume.
- Specify the Volume Mount Path on which you want to mount the PVC.
- Click “Add Row” in order to bind more PVCs.
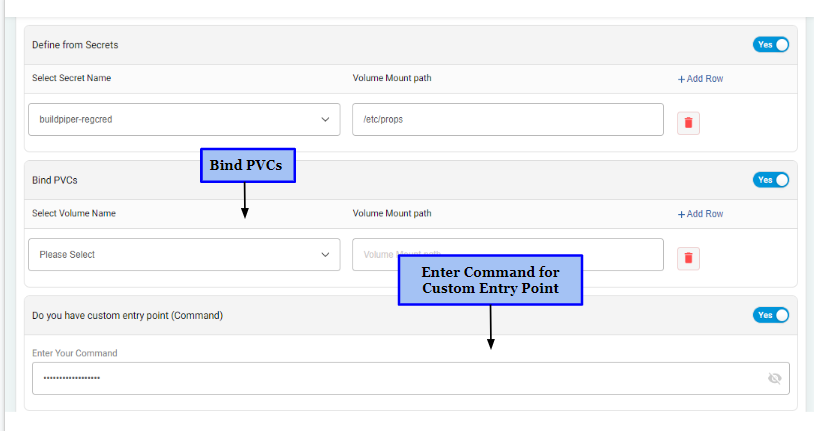
Add Custom Entry Point Command#
A custom entry point command is a command that is specified in a container image's Dockerfile or in a Kubernetes manifest. It is run as the primary process inside the container when the container is started. The custom command can be used to perform any necessary setup or initialization tasks before running the container's main application.
Here’s how you can add a Custom Entry Point Command.
- Choose “Yes” if there is a Custom Entry Point else a “No”.
- Enter the command if there exists a custom entry point.
- Click “Add Row” in order to add more commands.
- Finally click "Continue" to proceed further.